Beacon generation for android attacks
Test-oriented preview version
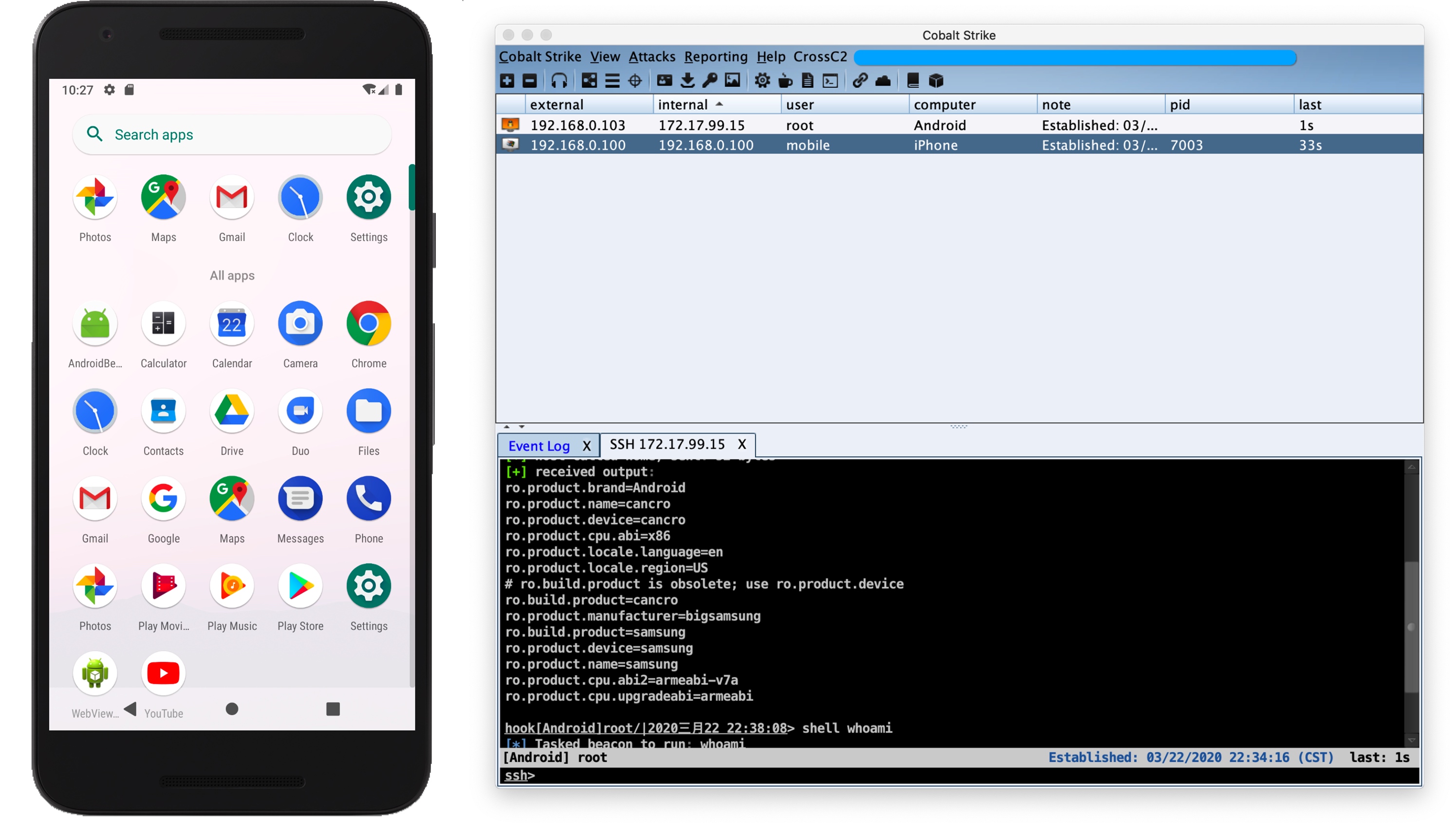
When creating a beacon through the .cna plugin, you can choose System as Android, Arch and select the specific target platform (armv7, arm64, x86).
Finally, a dynamic library .so file of the specified architecture will be generated. You can choose to package the dynamic library into the specified APK installation package or inject it into the specified App.
The final reconnect code will be executed automatically when the dynamic library is loaded. It should be noted that the ordinary app needs to be utilized by the application itself and the user has applied for network permissions before initiating the reconnect. If it is your own app, you need to consider matters related to the user's application for network, photo album, phone, recording and other permissions during development.
And during shell execution or file upload and download operations, if it exceeds its own permissions, the current process may be forced to kill by the system (not yet resolved)